Speakout 3ed C1-C2 Student's Book and Workbook with eBook and Online Practice Split 1
- 144bladzijden
- 6 uur lezen
Gold New Edition Gold New Edition follows the same approach as previous editions but has been revised and updated following extensive research with users throughout the world. It helps teachers to deliver stimulating, discussion-rich lessons with focused exam preparation. Each level of the series offers a strong emphasis on communicative practice and the development of natural speaking skills to build student confidence for exams and beyond.
Microsoft's cloud-based Azure Sentinel enables organizations to harness advanced AI for automated threat identification and response, addressing the complexities of traditional SIEM solutions. This guide, authored by three of Microsoft's top experts, provides a comprehensive roadmap for planning, deploying, and operating Azure Sentinel. Drawing from their hands-on experience with early adopters, they cover essential topics including configuration, data ingestion, rule development, incident management, and proactive threat hunting. Key insights include how to effectively utilize Azure Sentinel in today's dynamic cybersecurity landscape, understanding threat intelligence fundamentals such as attacker motivations and tactics, and exploring the platform's components and architecture. Readers will learn to ingest alert log data from critical services, build and validate analytical rules, and manage incident lifecycles within Security Operation Centers (SOCs). The experts emphasize the importance of proactive threat hunting to disrupt cyber kill chains and offer techniques to mitigate alert fatigue. Additionally, they demonstrate how to leverage programmable Jupyter notebooks for machine learning and data analysis, utilize Playbooks for Security Orchestration, Automation, and Response (SOAR), and automate responses to low-level events. Visualizations for trend spotting and integration with partners like Fortinet, AWS, and Palo Al
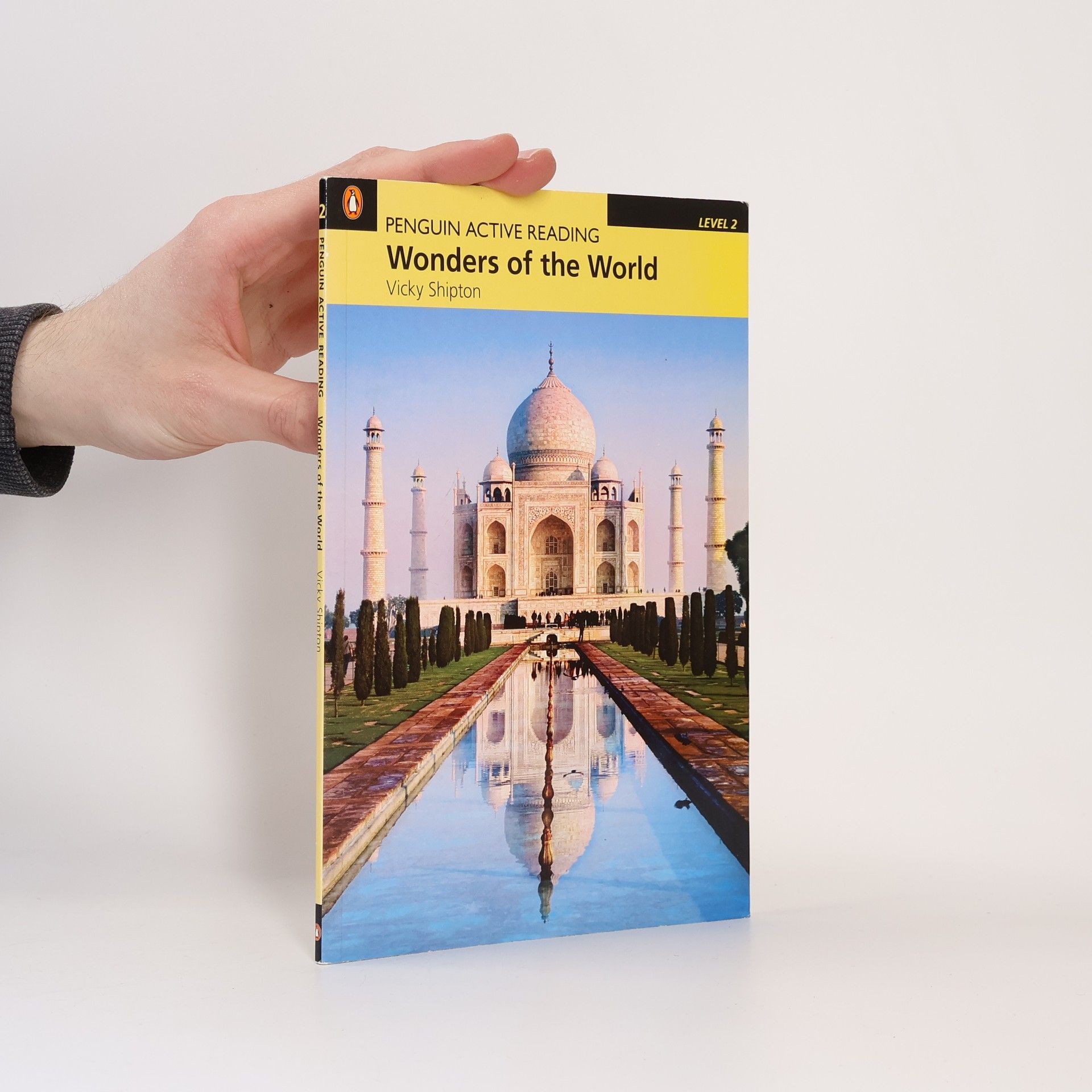
Around the world there are many beautiful places. There are famous buildings, old and new. Some are interesting; some are important. Some are the tallest or biggest in the world. The Great Wall, Machu Picchu, the Grand Canyon, the Taj Mahal...Which are your wonders of the world?
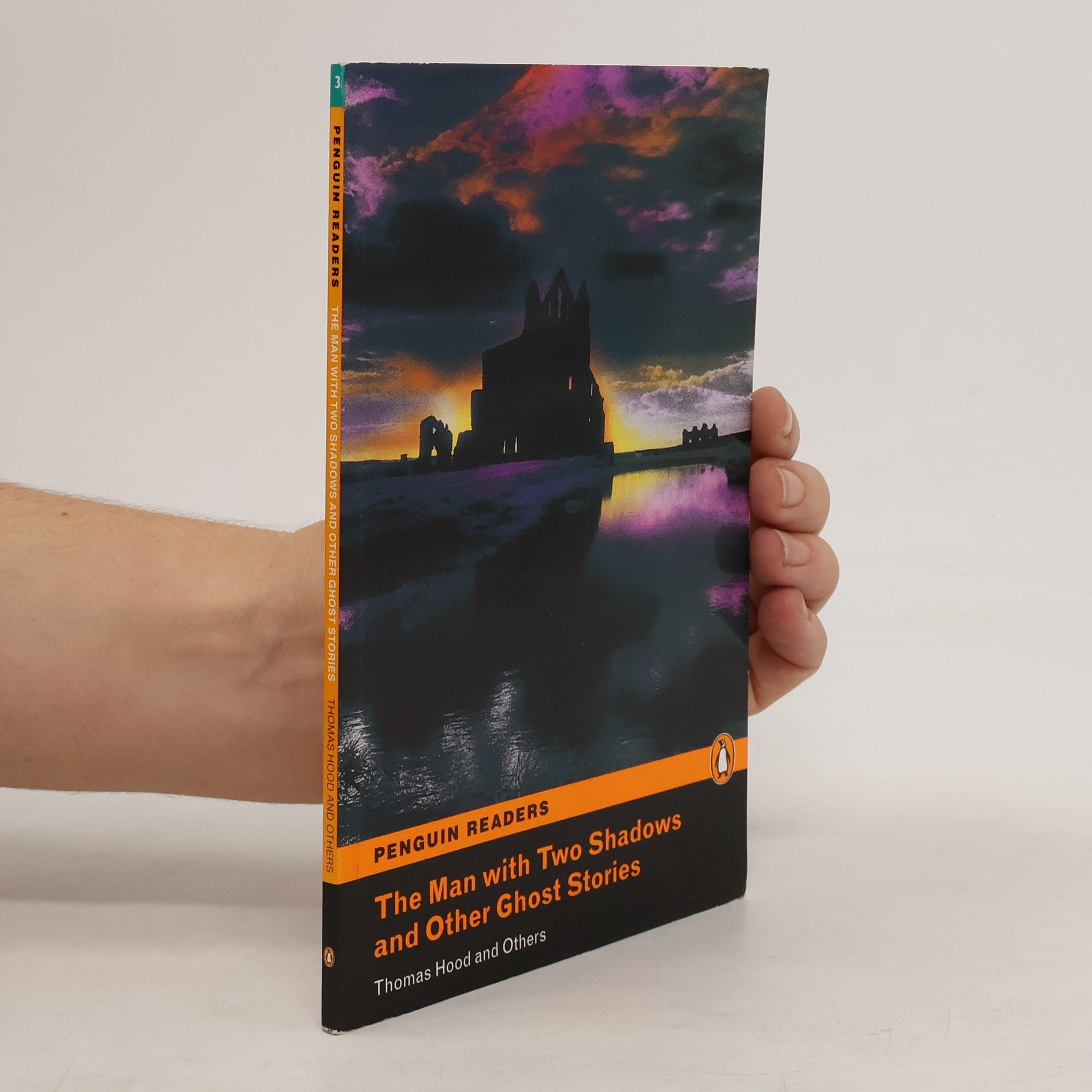
In these six stories, eerie events unfold as ghosts return for various purposes: to catch a murderer, bring misfortune, or warn of danger. Whether or not you believe in ghosts, these tales promise to captivate with their intriguing narratives.
Part of a multivolume work on the analysis of algorithms, this work provides a programmer's introduction to the MMIX, a RISC-based computer that replaces the original MIX, and describes the MMIX assembly language. It also presents material on subroutines, coroutines, and interpretive routines.
This book looks at how water can be found in three different forms: a liquid, a solid and a gas. Contains photographic images.
Das offizielle Übungsbuch entwickelt von Adobe-Mitarbeitern. Windows und Macintosh. Neu! Version 5.0. Mit CD-ROM!